24 April 2026 · articles
A Network Blueprint for Scaling Healthtech Securely
Discover how healthtech providers can scale secure clinical platforms for NHS trusts using a SASE architecture - without disrupting live services.
George Stern, Enterprise Connectivity & Security Specialist | Average Read Time: 6 minutes
Why healthtech growth needs secure foundations
Across the NHS and the wider health ecosystem, digital services are expanding rapidly. Remote patient monitoring, shared care records, and digital triage tools are being deployed to meet rising demand and reduce pressure on frontline staff. But many of the organisations building and hosting these platforms are running into the same problem: an infrastructure that was designed for a small, contained deployment and was never built to scale.
For healthtech providers serving NHS trusts, GP federations, and increasingly private healthcare organisations, the challenge is twofold. First, web-facing clinical applications are exposed, often protected by little more than basic perimeter security. Second, every new customer or service requires manual network changes that slow growth and introduce risk. The architecture becomes the bottleneck.
This use case sets out a practical framework for moving from a fragile, legacy-constrained setup to a scalable SASE architecture, without disrupting live clinical services.
A step-by-step blueprint
Phase 0: The Starting Point
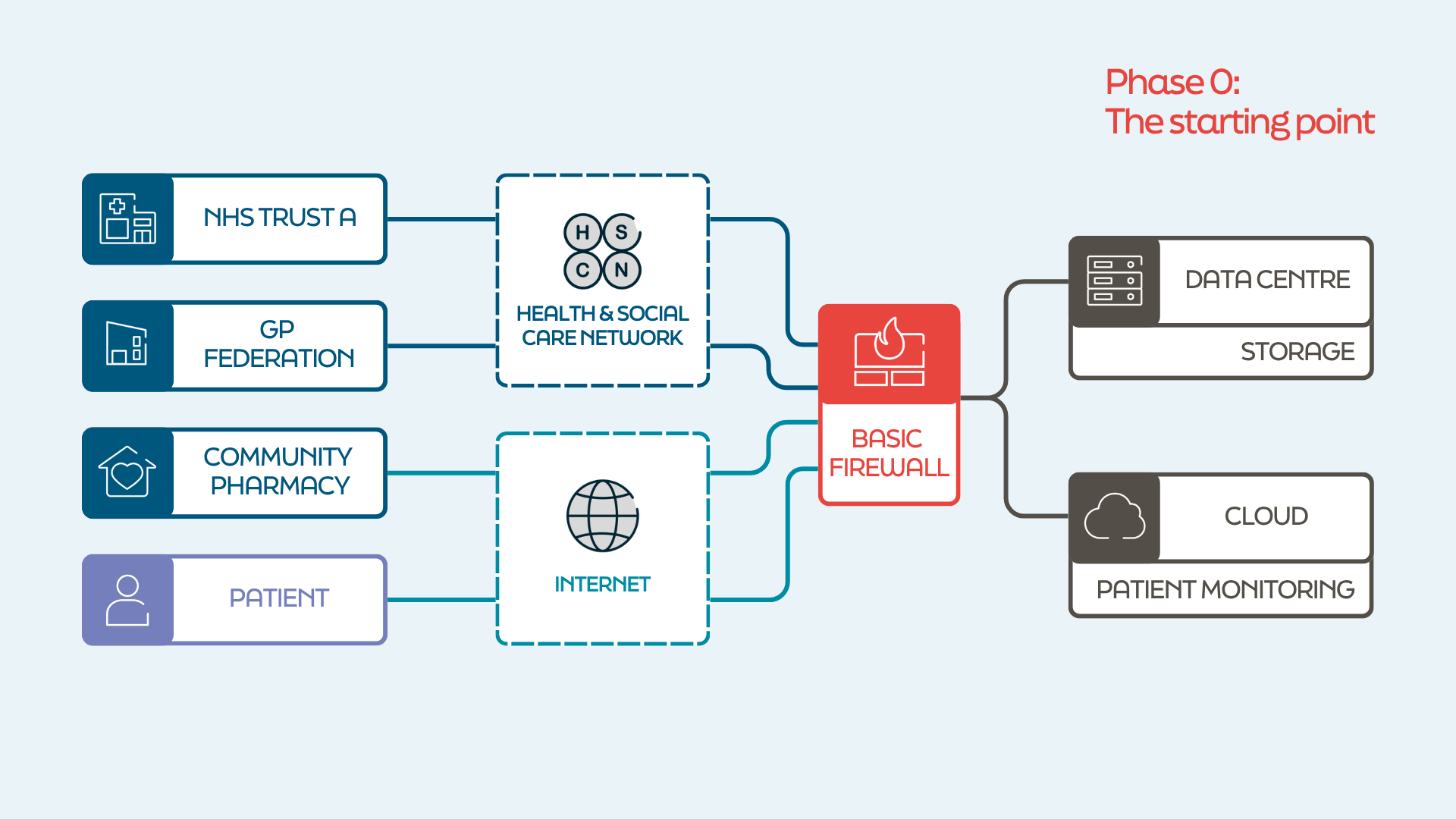
A healthtech provider operates a remote patient monitoring platform. Patients use it to log symptoms and condition updates; clinical staff at NHS trusts and GP practices monitor the data for changes that need intervention. The platform is hosted across a small cloud presence and an on-premises data centre.
Security is minimal: a basic perimeter firewall sits at the edge, but there is no web application firewall, no advanced threat protection, and no centralised security policy. The platform is accessed over a mix of HSCN and the public internet, with each connected trust or practice relying on its own point-to-point connectivity, manually configured.
At current scale, it works. But the web-facing application is exposed, onboarding a new trust takes weeks of network engineering, and the provider has no clear path to growing the platform without replicating the same fragile setup. The architecture is not complex - it is under-built, and that makes it both vulnerable and difficult to scale.
Phase 1: Introduce the SASE Gateway
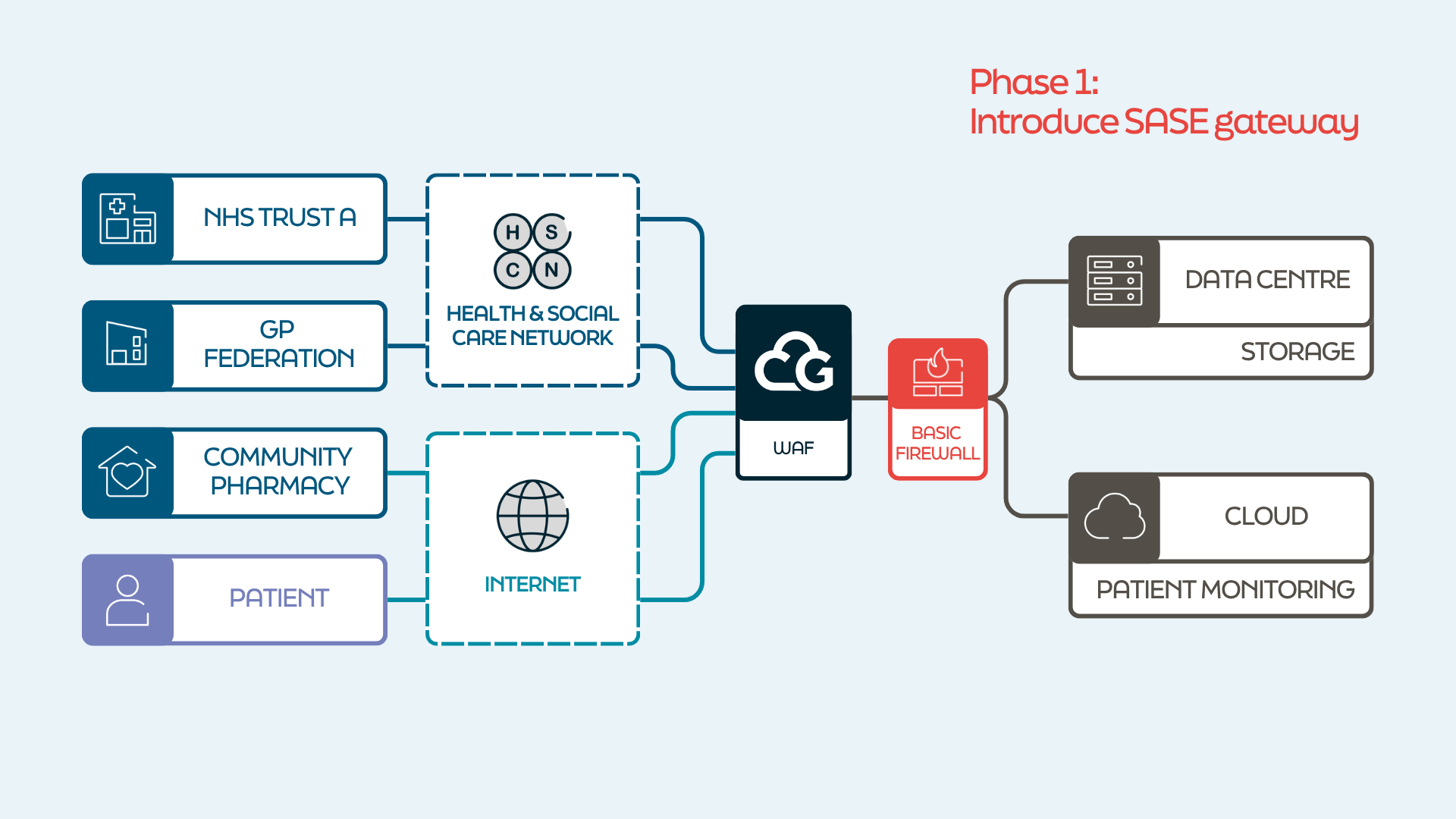 Cloud Gateway is deployed as a centralised SASE hub in front of the platform. All traffic - whether arriving over HSCN or the public internet - now routes through Cloud Gateway before reaching the application. The existing perimeter firewall stays in place during this phase, but Cloud Gateway immediately adds the protection that was missing: a cloud-delivered WAF, DDoS mitigation, and traffic inspection.
Cloud Gateway is deployed as a centralised SASE hub in front of the platform. All traffic - whether arriving over HSCN or the public internet - now routes through Cloud Gateway before reaching the application. The existing perimeter firewall stays in place during this phase, but Cloud Gateway immediately adds the protection that was missing: a cloud-delivered WAF, DDoS mitigation, and traffic inspection.
Nothing changes for end users or connected trusts. The application simply gains a proper security layer for the first time. Because Cloud Gateway supports HSCN natively, there is no need to bring in an additional connectivity partner - a single platform handles both public internet and health network traffic.
Phase 2: Consolidate Security
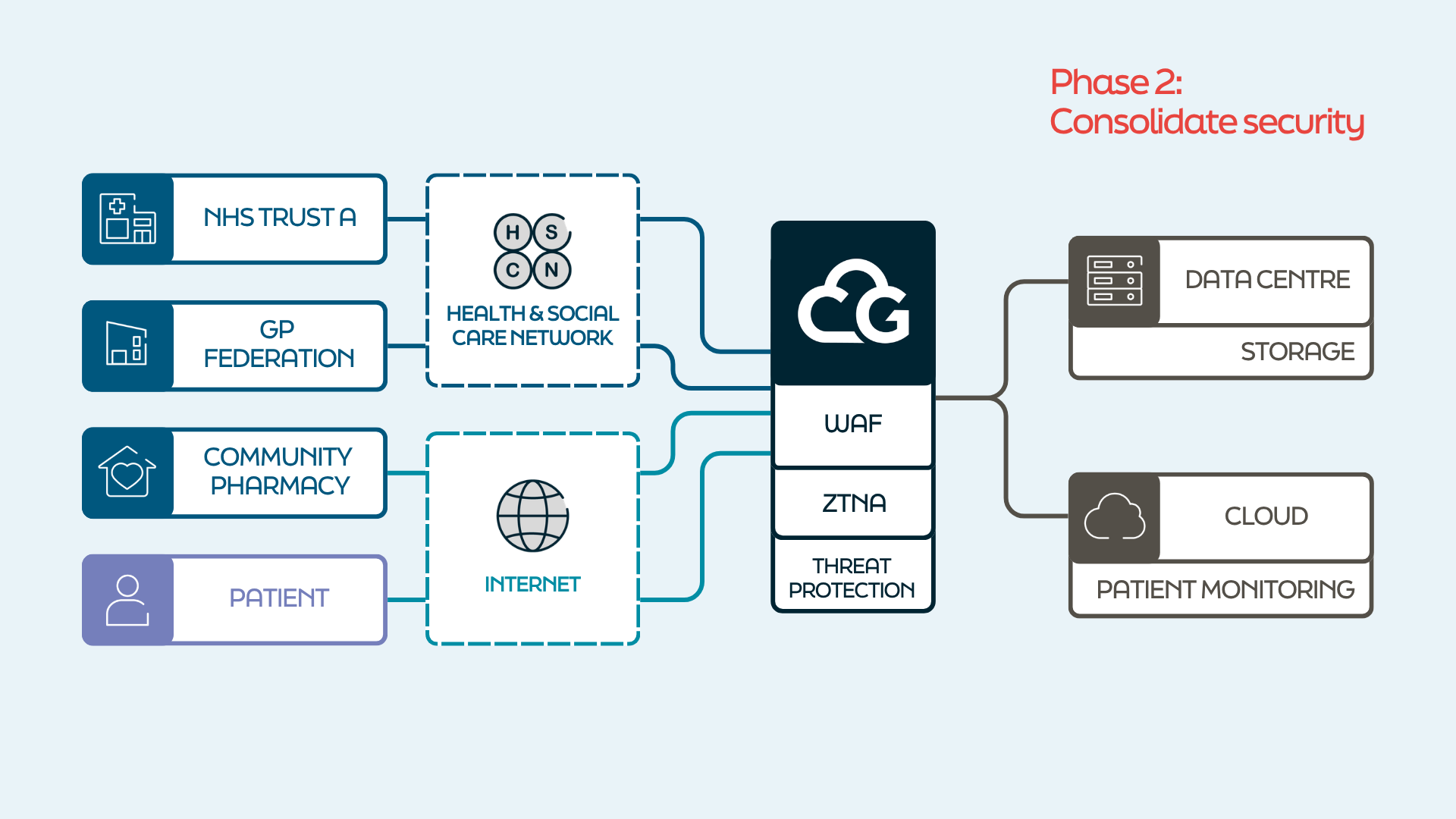 The SASE hub now takes over all security functions. WAF, zero trust access policies, TLS inspection, and threat prevention are all delivered through Cloud Gateway. The original perimeter firewall is decommissioned or reduced to a minimal monitoring role.
The SASE hub now takes over all security functions. WAF, zero trust access policies, TLS inspection, and threat prevention are all delivered through Cloud Gateway. The original perimeter firewall is decommissioned or reduced to a minimal monitoring role.
For the first time, the provider has a centralised, consistent security posture. Every trust, every GP practice, every remote clinician connecting to the platform goes through the same inspection and access controls. The web application is no longer directly internet-facing.
Compliance posture improves significantly. Where the organisation needs to go through DSPT assessments or other submissions, Cloud Gateway's experienced team can support them through the process, reducing the burden that often comes with adopting new infrastructure.
Phase 3: Hub and spoke: enable growth
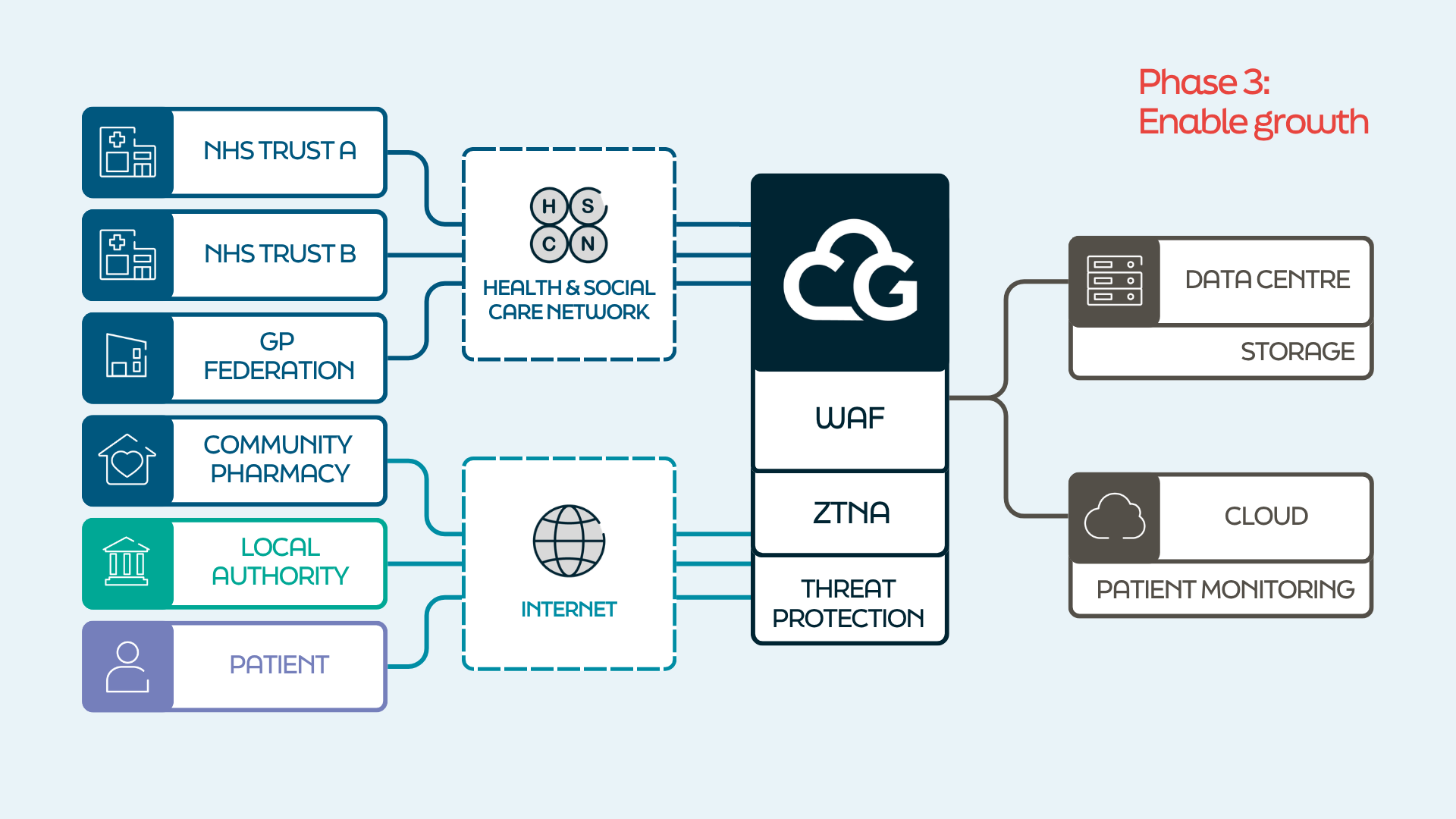 This is the phase where the architecture starts paying for itself. A new NHS trust wants access to the monitoring platform? It connects as a spoke through Cloud Gateway, with policy applied centrally. A private healthcare provider wants to onboard? Same process. There are no bespoke VPN tunnels to build, no firewall rules to hand-craft.
This is the phase where the architecture starts paying for itself. A new NHS trust wants access to the monitoring platform? It connects as a spoke through Cloud Gateway, with policy applied centrally. A private healthcare provider wants to onboard? Same process. There are no bespoke VPN tunnels to build, no firewall rules to hand-craft.
Onboarding a new consumer of the platform becomes a policy decision rather than a network engineering project. The provider can say yes to new customers without worrying about whether the infrastructure can handle it. Growth is no longer gated by the network.
Phase 4: Scale and extend
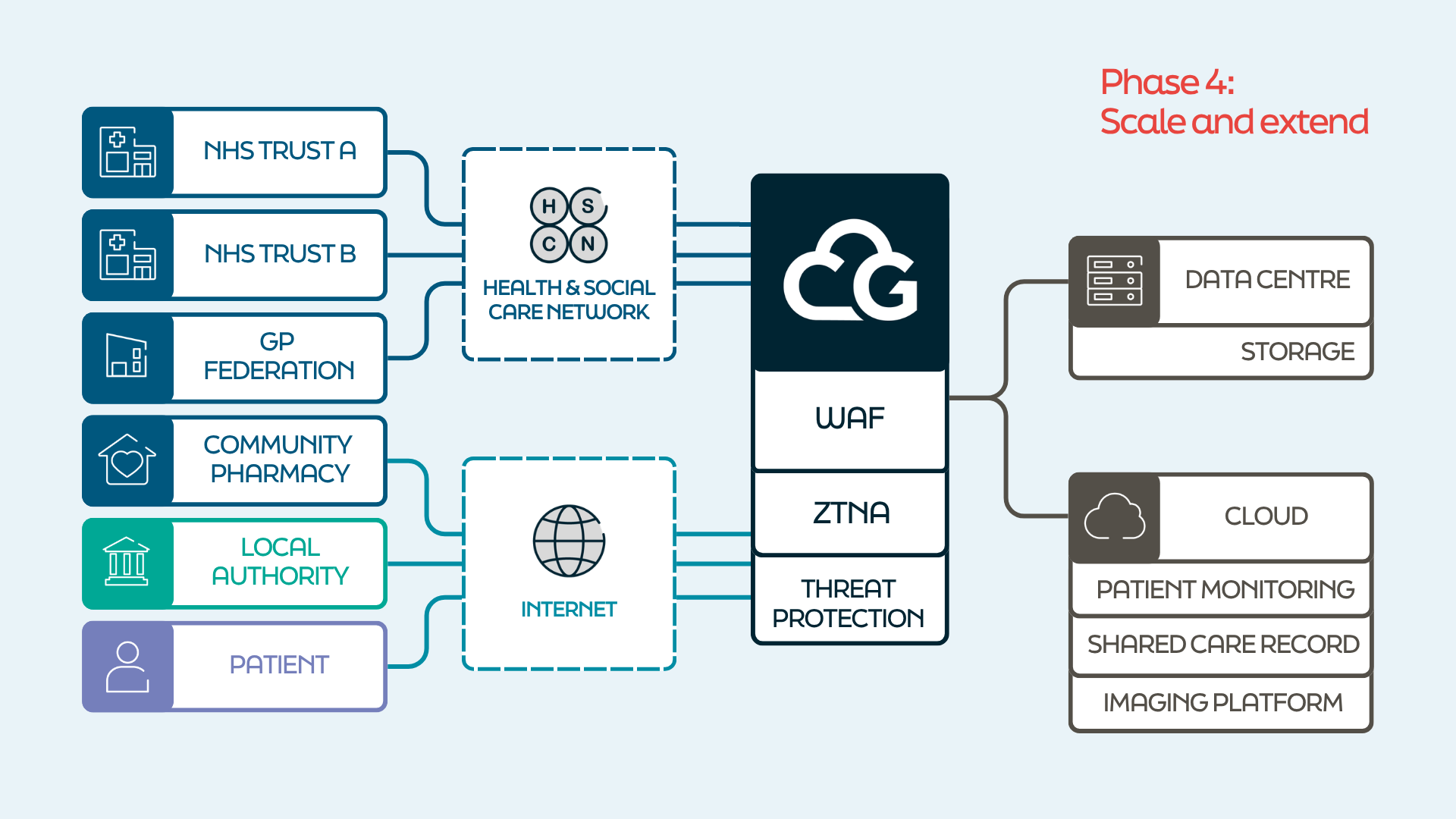 With a scalable, secure architecture in place, the provider is no longer limited to a single application. A shared care record, a diagnostic imaging viewer, or a secondary monitoring tool can all be published through the same SASE hub. Each new application inherits the same security posture, the same access controls, and the same compliance framework - without duplicating infrastructure.
With a scalable, secure architecture in place, the provider is no longer limited to a single application. A shared care record, a diagnostic imaging viewer, or a secondary monitoring tool can all be published through the same SASE hub. Each new application inherits the same security posture, the same access controls, and the same compliance framework - without duplicating infrastructure.
With the platform now running through a unified architecture, there is also an opportunity to optimise the underlying cloud environment. Cloud Gateway works with a partner network that can support cloud optimisation - ensuring the provider is not overspending on compute, storage, or connectivity as the platform scales.
The platform now enables:
Publishing new clinical applications to existing customers without re-engineering connectivity
Onboarding new customer organisations in days rather than weeks
Maintaining a consistent compliance and security baseline across every service
Scaling into new regions or care settings without redesigning the network
The architecture that once held the organisation back is now the thing that lets it grow.
What this means for healthtech
NHS trusts and their technology partners are under pressure to digitise clinical pathways quickly, but the tolerance for security incidents in healthcare is zero. By treating network architecture as a strategic enabler rather than a technical dependency, healthtech providers can turn infrastructure from a constraint on growth into a platform for it - protecting patients' data while making it easier, not harder, to expand the services that rely on it.
Talk to the Cloud Gateway team about a phased approach to secure cloud transformation.
Tell us your network and cloud challenges. We’re here to help.
Speak to one of the Cloud Gateway team

/f/148396/1500x1000/87001c38e6/healthtech-featured-image.png)
/f/148396/2250x1500/18e9b623d7/cgw-logo-nhs-header.png)
/f/148396/1500x1000/a42e4d03f6/nhs-header-image-compressed.png)
/f/148396/1500x1000/782663a958/dashboard-cgw-header.png)